Many enterprises venture into clouds and find the landscape of cloud networking very different from on-prem. Multi-homed devices such as routers and firewalls when deploy to the cloud also are having challenges to insert themself into traffic path, particularly due the reasons listed below. This in turn slows down the enterprises adoption speed to the cloud. Let’s take a look what some of these challenges are:
Continue readingCategory Archives: aviatrix
Terraform init failed to download providers
One of our customers are looking to use Aviatrix to automatic their self-service process for AWS China region.
The issue they are running into, was the terraform init would fail 50% of time. Is there anything we can do to help in this situation?
Continue readingDeploy Aviatrix Metered Controller in Azure
This is a quick write up of deploying Aviatrix Metered Controller in Azure
Integrate Okta IdP with Aviatrix controller
In this blog, I will show you step by step integrating Okta IdP (identity provider) with Aviatrix controller.
Continue readingSecure Aviatrix Controller with Azure Application Gateway V2
Aviatrix controller is already hardened. You may further lock it down with Settings -> Controller -> Access Security -> Controller Security Group Management. The controller would be protected by Security Group allowing access only from Aviatrix Gateways. Customer can add their own egress public IPs and CoPilot public IPs to security group, allowing inbound HTTPs access to the Aviatrix controller.
Enterprises already utilizing Azure Application Gateway/ WAF may want to place the Aviatrix controller behind it, for tighter security. This blog post shows how to place the Aviatrix controller behind Azure Application Gateway/WAF
Continue readingAdd SSL Certificate to Aviatrix Controller
When first launched Aviatrix controller from marketplace, the Aviatrix controller give itself a self-signed certificate, and you have to use https://controller-ip to access it, which may not meet compliance requirement.
This blog will talk about getting a public trusted SSL certificate for Aviatrix controller.
Continue readingEnable private connectivity to workloads deployed in multiple default VPCs – Part 1
Scenario: One of our customers are primary in Azure, after merger and acquisitions, them acquired hundreds of AWS accounts, where workloads are deployed to default VPCs, which all have this address space: 172.31.0.0/16
They are looking for a solution to provide bi-directional private connectivity to these workloads in AWS from Azure without overhead of route management, also provide visibility to the traffic.
Continue readingEnable private connectivity to workloads deployed in multiple default VPCs – Part 2
Scenario: One of our customers are primary in Azure, after merger and acquisitions, them acquired hundreds of AWS accounts, where workloads are deployed to default VPCs, which all have this address space: 172.31.0.0/16
They are looking for a solution to provide bi-directional private connectivity to these workloads in AWS from Azure without overhead of route management, also provide visibility to the traffic.
Continue readingTechTalk | Securing Cloud Egress—The Easy Way
When operating in the cloud, enterprises often struggle with how to gain control of network traffic leaving their environments in a centralized, cost-effective, and CSP-agnostic way.
In this webinar, you’ll learn how to make cloud egress architecture simple, repeatable, and automated—including how to:
- Gain visibility and control of internet-destined traffic in a cost-effective way (FQDN, subtopics distributed, centralized)
- Insert next-generation firewalls into internet-outbound traffic and deal with thousands of route entries
- Scale up and scale out your egress firewalls in an active manner and retain existing flows
- Plus, the benefits of leveraging Aviatrix FireNet and ThreatIQ, ThreatGuard, and Anomaly Detection.
Use terraformer to import AWS resources in linux
I’ve come to a situation to import existing resources into terraform, and this tool seems to be interesting:
https://github.com/GoogleCloudPlatform/terraformer
The following example is in Linux, and my terraform installation is at /user/bin/terraform
$ which terraform
/usr/bin/terraformBy looking up the executable in following link:
https://github.com/GoogleCloudPlatform/terraformer/releases
Since I’m running Linux and need to import resources in AWS, I’ve downloaded:
terraformer-aws-linux-amd64 to /user/bin
cd /usr/bin
sudo wget https://github.com/GoogleCloudPlatform/terraformer/releases/download/0.8.19/terraform
er-aws-linux-amd64Verified that I do have AWS credentials in environment variables
$ cat ~/.profile
# environment variables
export AWS_ACCESS_KEY_ID='****'
export AWS_SECRET_ACCESS_KEY='****'Create a new folder for terraform files
mkdir ~/terraformerCreate providers.tf
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 4.0"
}
}
}
# Configure the AWS Provider
provider "aws" {
}Run terraform init
$ terraform init
Initializing the backend...
Initializing provider plugins...
- Finding hashicorp/aws versions matching "~> 4.0"...
- Installing hashicorp/aws v4.5.0...
- Installed hashicorp/aws v4.5.0 (signed by HashiCorp)
Terraform has made some changes to the provider dependency selections recorded
in the .terraform.lock.hcl file. Review those changes and commit them to your
version control system if they represent changes you intended to make.
Terraform has been successfully initialized!While I’m trying to use Terraformer, I’m getting an error:
$ terraformer-aws-windows-amd64.exe import aws --resources=s3
2022/03/18 11:57:29 aws importing default region
2022/03/18 11:57:30 aws importing... s3
2022/03/18 11:57:34 aws error initializing resources in service s3, err: no EC2 IMDS role found, operation error ec2imds: GetMetadata, exceeded maximum number of attempts, 3, request send failed, Get "http://169.254.169.254/latest/meta-data/iam/security-credentials/": dial tcp 169.254.169.254:80: connectex: A socket operation was attempted to an unreachable network.
2022/03/18 11:57:34 aws Connecting....After some research and the workaround is:
$ terraformer-aws-windows-amd64.exe import aws --resources=s3 --regions=us-west-1 --profile=""
2022/03/18 11:59:11 aws importing region us-west-1
2022/03/18 11:59:13 aws importing... s3
2022/03/18 11:59:16 aws done importing s3
2022/03/18 11:59:16 Number of resources for service s3: 3
2022/03/18 11:59:16 Refreshing state... aws_s3_bucket.tfer--pan-bootstrap-jye
2022/03/18 11:59:16 Refreshing state... aws_s3_bucket.tfer--cf-templates-6vv0zllrvrqt-us-west-1
2022/03/18 11:59:16 Refreshing state... aws_s3_bucket.tfer--bootstrap-dfa5077a6c367b5a
2022/03/18 11:59:22 Filtered number of resources for service s3: 3
2022/03/18 11:59:22 aws Connecting....
2022/03/18 11:59:22 aws save s3
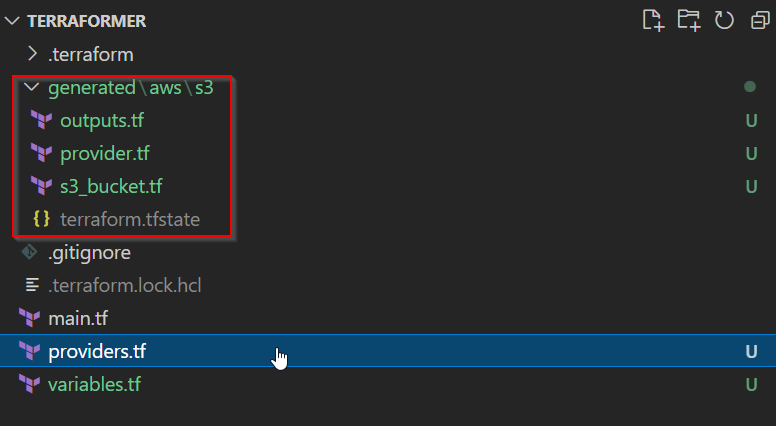
2022/03/18 11:59:22 aws save tfstate for s3new folders gets created with generated terraform code and state file: