I’ve come to a situation to import existing resources into terraform, and this tool seems to be interesting:
https://github.com/GoogleCloudPlatform/terraformer
The following example is in Linux, and my terraform installation is at /user/bin/terraform
$ which terraform
/usr/bin/terraformBy looking up the executable in following link:
https://github.com/GoogleCloudPlatform/terraformer/releases
Since I’m running Linux and need to import resources in AWS, I’ve downloaded:
terraformer-aws-linux-amd64 to /user/bin
cd /usr/bin
sudo wget https://github.com/GoogleCloudPlatform/terraformer/releases/download/0.8.19/terraform
er-aws-linux-amd64Verified that I do have AWS credentials in environment variables
$ cat ~/.profile
# environment variables
export AWS_ACCESS_KEY_ID='****'
export AWS_SECRET_ACCESS_KEY='****'Create a new folder for terraform files
mkdir ~/terraformerCreate providers.tf
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 4.0"
}
}
}
# Configure the AWS Provider
provider "aws" {
}Run terraform init
$ terraform init
Initializing the backend...
Initializing provider plugins...
- Finding hashicorp/aws versions matching "~> 4.0"...
- Installing hashicorp/aws v4.5.0...
- Installed hashicorp/aws v4.5.0 (signed by HashiCorp)
Terraform has made some changes to the provider dependency selections recorded
in the .terraform.lock.hcl file. Review those changes and commit them to your
version control system if they represent changes you intended to make.
Terraform has been successfully initialized!While I’m trying to use Terraformer, I’m getting an error:
$ terraformer-aws-windows-amd64.exe import aws --resources=s3
2022/03/18 11:57:29 aws importing default region
2022/03/18 11:57:30 aws importing... s3
2022/03/18 11:57:34 aws error initializing resources in service s3, err: no EC2 IMDS role found, operation error ec2imds: GetMetadata, exceeded maximum number of attempts, 3, request send failed, Get "http://169.254.169.254/latest/meta-data/iam/security-credentials/": dial tcp 169.254.169.254:80: connectex: A socket operation was attempted to an unreachable network.
2022/03/18 11:57:34 aws Connecting....After some research and the workaround is:
$ terraformer-aws-windows-amd64.exe import aws --resources=s3 --regions=us-west-1 --profile=""
2022/03/18 11:59:11 aws importing region us-west-1
2022/03/18 11:59:13 aws importing... s3
2022/03/18 11:59:16 aws done importing s3
2022/03/18 11:59:16 Number of resources for service s3: 3
2022/03/18 11:59:16 Refreshing state... aws_s3_bucket.tfer--pan-bootstrap-jye
2022/03/18 11:59:16 Refreshing state... aws_s3_bucket.tfer--cf-templates-6vv0zllrvrqt-us-west-1
2022/03/18 11:59:16 Refreshing state... aws_s3_bucket.tfer--bootstrap-dfa5077a6c367b5a
2022/03/18 11:59:22 Filtered number of resources for service s3: 3
2022/03/18 11:59:22 aws Connecting....
2022/03/18 11:59:22 aws save s3
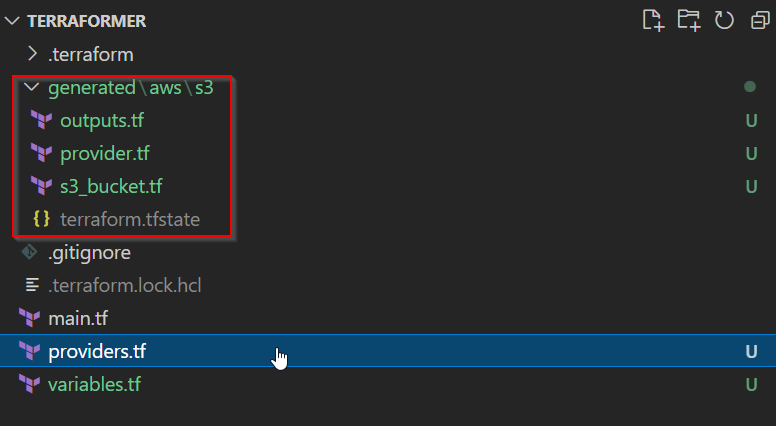
2022/03/18 11:59:22 aws save tfstate for s3new folders gets created with generated terraform code and state file: